Take Survey For Chance to Win $50 Amazon Gift Certificate
One of the most powerful and under appreciated features of Amazon Web Services in the security group. When you launch an instance on AWS, it is automatically added to a default security group that protects it from unauthorized traffic. The default security group allows no inbound traffic, all outbound traffic, and allows full access between instances in the same security group. By creating or modifying security groups, you can support sophisticated access rules for your infrastructure that give you the flexibility of your own firewalls without the operational cost of managing physical infrastructure.
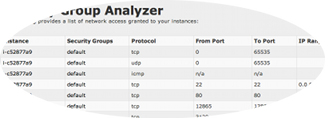
The one downside to security groups though is in the limited reporting available in the AWS Console (which as a general rule, can be said about all features in the AWS Console). The console is good for creating, editing and deleting individual security groups, but is ineffective for understanding even moderately sophisticated configurations.
The other day while on vacation down in Truro, I wrote a simple tool to analyze and report on security group rules across your instances. The work took less than an hour, but allowed be to identify a couple unintended permissions I had granted to my personal infrastructure. I published the tool as a free service this morning at apps.cloudpercept.com, so if you have an interest, please take a look. Feedback is of welcome.
Related Posts: Amazon Reserved Instance Calculator, Movement in the Cloud